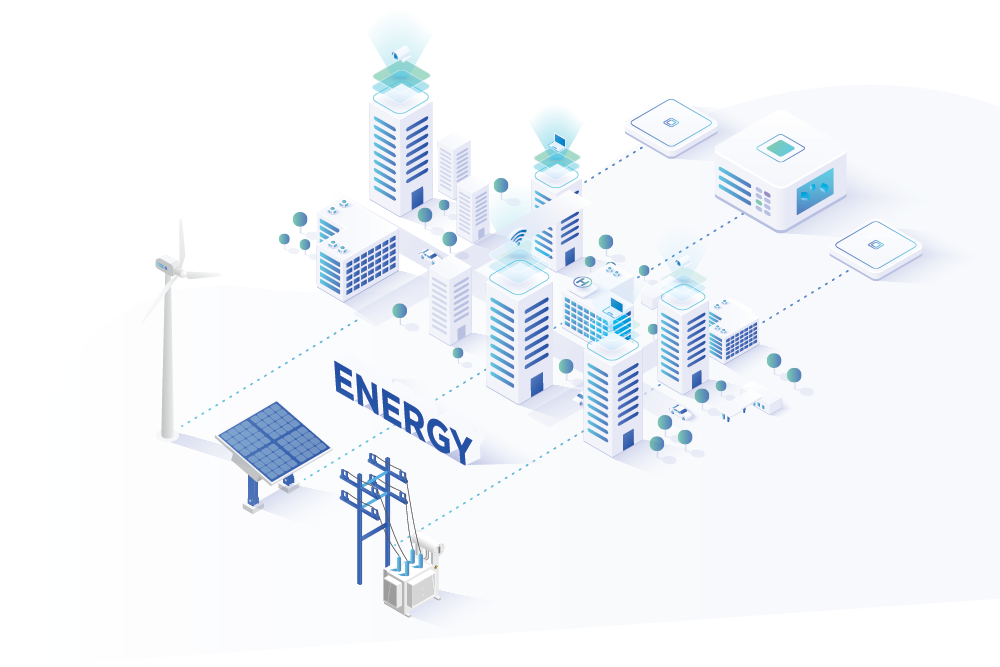
Overview
ARX For Energy
The subject of cyber security in the energy sector should be of perhaps great concern to all countries across the globe. Over the last couple of years, cyber-attacks on critical infrastructure have surged and the potential repercussions are significant. A loss of data is concerning, but a loss of electricity and water is catastrophic to both business and society.
The sector also plays a key role in the global economy. In 2019, the energy industry alone generated about $238 billion in revenue, an increase of about $25 billion from 2017. Since the power sector is interconnected to the larger infrastructure of a city and thereby a country, it has been a constant target of cybercriminals and digital fraud perpetrators.
Threats
Challenges Galore
The energy sector cyber threat landscape is quickly evolving and expanding, with more recurrent attacks, with numerous and diverse threat actors, and progressively urbane malware and tools that are widely available and sometimes extensively organised. An absence of manpower and the pure number of dealers and transactions, makes this sector vulnerable.

Interdependent Supply Chain
As companies have streamlined their operations, supply chains are becoming more integrated and interdependent. If one part of a supply chain is interrupted, then it has the power to shut down the entire chain. The cyber supply chain accountability and ownership is challenging in this sector. They may touch diverse departments, including supply and procurement, warehouse management, corporate information security, cloud and infrastructure, legal, IT, and OT (Operational Technology).
Third-party involvement
Power companies purchase information, hardware, software, services, and more from third parties across the globe. Cyber criminals can easily introduce compromised components into a system or network, unintentionally or by design, at any point in the system’s life cycle. This may be through software updates or “patches”, which are downloaded frequently, or through firmware that can be manipulated to include malicious codes for exploitation at a later date.
Supplier problems
In some cases, suppliers might not even give access to the energy companies and some are adamant to not adopt secure practices. In totality, most of the power companies have little or no control over the activities of the suppliers.
Larger implications
There are cybercriminals who often target power grids motivated by financial goals, such as ransom ware or intellectual property theft, or sometimes even broader economic and social harm.
Solutions
The ARX Advantage
Single sign-on
In the energy sector, accessing the network from remote locations is seen as a major disadvantage. When there are multiple passwords for a network system, users often end up keying in the password again and again, which makes the system vulnerable to cyber-attacks.
Single sign-on
In the energy sector, accessing the network from remote locations is seen as a major disadvantage. When there are multiple passwords for a network system, users often end up keying in the password again and again, which makes the system vulnerable to cyber-attacks. Also, when the sector is as important as the energy sector, multiple passwords can only be time-consuming. An easy solution to fix this – using a single user id and password across all systems that the user is going to use.
With the Single Sign-On (SSO), instead of a password for every application, users have one password to remember. With that single sign-on, they get access to all their applications. SSO assures that the users have a strong password. Also, it eliminates the need of a middleman to reset passwords time and again.
SSO makes the energy industry more secure, and life for the users easier. With SSO,
- We provide efficient, cost-effective and nimble identity infrastructure for IT at the organisation
- Help users increase their productivity as they can seamlessly connect to multiple IT resources using the same credentials
- Mitigate risk of having lost, weak and shared passwords, by restricting access to services via various intelligent integrations like OAuth, SAML, and RSA
Enforce Strong Authentication
Cyber-security in the energy sector has become particularly important, since cyber threats in the energy space does not only limit itself to the internet, but also affects the physical world.
Enforce Strong Authentication
Cyber-security in the energy sector has become particularly important, since cyber threats in the energy space does not only limit itself to the internet, but also affects the physical world. In an era of digitalisation, energy companies are embracing Internet of Things (IoT) in order to efficiently connect with remote locations and multiple vendors. This leaves the security network at risk. One effective way energy companies can reduce the risk of cyber attack is to ensure strong authentication mechanisms for authorising individuals to access systems and facilities.
A strong Multi-Factor Authentication (MFA) system can prevent such attacks. It creates multiple layers of security, resulting in efficient and diligent authentication. This ensures that the user requesting access is actually who they claim to be.
With MFA, a cybercriminal may steal one credential, but will be thwarted by having to verify identity in a different manner. MFA is an effective way to provide enhanced security for all your IT resources including cloud, on-premise and mobile.
- We help enable ‘MFA Everywhere’ on-premise with our strong integration support
- Starting from simple question-answers to fingerprint authentication and random pin generation device, any of these can be deployed for the MFA needs. All these can be configured using easy steps
User Management
According to a new study from The Ponemon Institute, Energy & Utilities sector has spent $11.54M on insider threats in the last two years, which is a 12.8% increase.
User Management
According to a new study from The Ponemon Institute, Energy & Utilities sector has spent $11.54M on insider threats in the last two years, which is a 12.8% increase. This sector is highly collaborative with a number of supply chains and third parties involved. In fact, a report on digital fraud states that the energy sector faces the highest consequential costs when it comes to digital fraud, outpacing the banking and finance sector, as well as many others.
In an industry where multiple employees and vendors are involved, there is a lot of data which is at risk. Leveraging automated user management streamlines role-based access control. Along with security suite features like authentication, access controls, privileges, entitlements, single sign-on & security policies and activity auditing across organisation, the organisation can also create an error-free workflow as well, which will define the role of each and every employee.
With a better User Management,
- Bulk onboarding with exact required privileges can be performed easily
- Deboarding at ease without any worries
- With maker-checker workflow, one can be absolutely sure who is going to do what
Visibility, Detection and Response
The energy sector is highly complex – the supply chains differ from one country to another, various stakeholders and the types of consumers (individuals, businesses),
Visibility, Detection and Response
The energy sector is highly complex – the supply chains differ from one country to another, various stakeholders and the types of consumers (individuals, businesses), those dependent on continuous supplies of energy such as hospitals, links in the food chain and transport — all these individuals and organisations are vulnerable to cyber-attacks. A recent paper by Marsh & McLennan lays out the risks involved in this sector, and the way in which they increase owing to the internet-based relationships within the energy industry, and between suppliers and consumers.
This is where ARX can help the firm. With lifecycle managed users, Access Controls and Authorisation Access can be easily managed and mapped. Along with a maker-checker workflow, the firm can keep track of who is doing what. With a clear visibility and detection mechanism in place, they can also respond to any threat, which otherwise could leave them exposed.
- One-stop shop for single login for users and one unified identity infrastructure for IT
- Integration with existing security tools
- Maker-checker workflow helps identify unusual and suspicious behaviours
- ARX API services can be used to enrich and extend the cyber security ecosystem; this is supported by helping to generate extensive reports for a deep dive into what is happening
- Can be easily integrated with the existing application with ARX using REST APIs for:
- Primary Authentication
- Multi-Factor Authentication
- User Management
- Password Management
- Validate and Get Entitlement
- Role-based access control –granular application-level access controls using entitlement policies that can be assigned to roles
- Users get access to resources based on their role. Access rights are grouped by role name, and access to resources is restricted to users who have been authorised to assume the associated role
Sign up for a
demo today!
Let us take you through our state of the art ARX suite of security services which will provide you with end to end security for user identification, authentication, single sign on, authorization and entitlements.